Redis is an open-source in-memory data structure store, which is a very popular selection among developers due to its variety of data structures that satisfy all application needs. The Remote Dictionary Server or Redis, is mainly implemented for caching purposes, as a message broker and also utilized as a NoSQL Key-Value database for different use cases. It is also a BSD licensed open-source, in-memory data structure store – where data is not written to disk but kept in volatile RAM. Product engineering and software development companies have found great potential in Redis as its advanced capabilities in modern applications enables search, messaging, streaming, graph, and other innovative capacities. It is also used as a database, cache, and message broker.
Therefore, whether you are a developer interested in learning Redis or a professional thinking about implementing Redis in your enterprise, our article can provide exactly what you’re looking for! So, let’s begin!
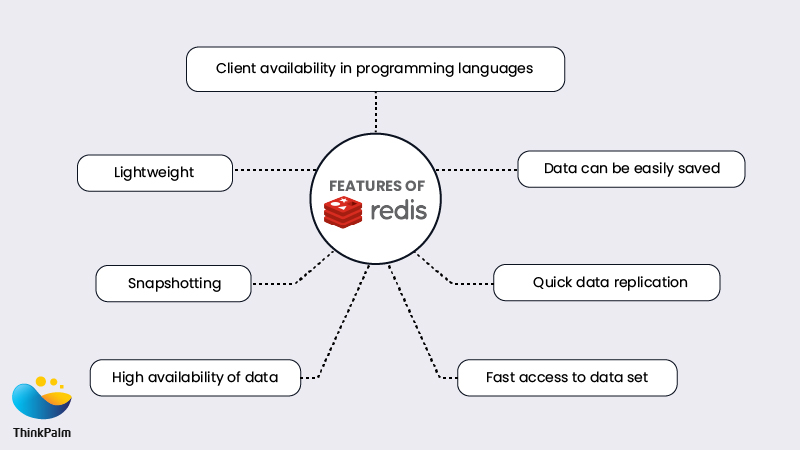
Often referred to as the “Leatherman of Databases”, the simple yet flexible design philosophy of Redis makes it an effective choice in solving a multitude of demanding data processing tasks for software development companies. Redis data structures resolve very complex programming problems with simple commands executed within the data store, reducing coding effort, increasing throughput, and reducing latency. Here are a few features of Redis!
Fast: Redis is extremely fast as it stores the whole dataset in primary memory.
Persistence: Based on the number of updates or elapsed time, data can be asynchronously saved to disk.
Data replication: Master-slave cache nodes can be set up. Slave node always listens to master i.e. when the master node is updated, the slave is updated automatically.
Clients available in all popular programming languages: Redis client API is developed in almost all popular languages like C, C++, Java, JavaScript, Python, etc.
Lightweight: Redis is written in ANSI C, with no external dependencies.
Snapshotting: Redis by default stores snapshots of your data in dumb.rdb file. In the case of server restart, Redis will load the data from a backup file and put them into memory.
High Availability: To ensure high availability of data, there is a built-in support for asynchronous master/slave replication, for which Redis Sentinel can be used.
Redis Sentinel is the high availability solution offered by Redis, . In case of a failure in your Redis cluster, Sentinel will automatically detect the point of failure and bring the cluster back to stable mode without any human intervention. In other words, Redis Sentinel is a system that can resist Redis deployment without human intervention.
Caching is a technique used to accelerate application response times and help applications scale by placing frequently needed data very close to the application. Redis, an open-source, in-memory, data structure server is frequently used as a distributed shared cache (in addition
to being used as a message broker or database) because it enables true statelessness for an applications’ processes while reducing duplication of data or requests to external data sources. Other than caching, here are a few other capabilities of Redis Sentinel.
Monitoring: Check all instances i.e. whether master and slave are working properly.
Notification: If one of the Redis instances are not working as expected, Sentinel can notify system administrators or another program through an API.
Automatic failover: If the master is not working as expected, Sentinel promotes one of the slaves as master and then make the additional slaves use the new master.
Sentinel is the source of authority for clients. The client connects to Sentinel for asking the address of the current Redis master.
The idea of Sentinel is that it’s an independent node that keeps track of the master node and other slave nodes. In a master-slave scenario, the master is meant for writing and slaves are for reading. When the master goes down, a slave node will become a master and it will have the capability to do both reading and writing. All other slaves will become slaves to the new master.
The Redis project does not officially support windows. However, Redis has been ported to Windows (64 bit) by Microsoft Open Technology Project. The default installation folder is ‘C:\Program Files\Redis’.
This example consists of 3 Redis instances and one Sentinel instance. For the sake of easiness, all these instances are hosted in one machine itself.
Redis_Master = Master instance
Redis_Slave1 = Slave 1 instance i.e. slave of Redis_Master
Redis_Slave2 = Slave 2 instance i.e. slave of Redis_Master
Sentinel = Sentinel instance
To deploy 3 Redis instances, create three copies of ‘redis.windows.conf’ file in ‘C:\Program Files\Redis’ as below
redis.windows-service-redis1.conf
redis.windows-service-redis2.conf
redis.windows-service-redis3.conf
To deploy Sentinel instance, create sentinel.conf file in ‘C:\Program Files\Redis’ as below
sentinel.conf
port 26379
sentinel monitor Redis_Master 127.0.0.1 6379 1
sentinel down-after-milliseconds Redis_Master 30000
sentinel parallel-syncs Redis_Master 1
sentinel failover-timeout Redis_Master 180000
The syntax for above configuration is :
sentinel monitor MasterName RedisMasterServerIP RedisMasterPort Quorum
sentinel down-after-milliseconds MasterName DownTimeout
sentinel failover-timeout MasterName FailoverTimeout
sentinel parallel-syncs MasterName ConcurrentServerSync
where
Line 1 – tells the master to be monitored. The quorum is used to detect failures. When the master is not reachable, the number of sentinels in the quorum should agree about it.
Line 2 – master will be considered as down when it’s not reachable for the Sentinel for the time specified in milliseconds.
Line 3 – The timeout in milliseconds indicates the time that Sentinel will wait after a failover before starting a new failover.
Line 4 – The number of slaves that can synch with the new master at the same time after failover.
Let’s create 3 Redis instances and one Sentinel instance as windows service. The below commands needs to be run in command prompt (Run as administrator) to do the same:
Redis Sentinel : sc create Redis_Sentinel DisplayName= “Redis_Sentinel” binPath= “\”C:\Program Files\Redis\redis-server.exe\” –service-run \”C:\Program Files\Redis\sentinel.conf\” –sentinel
Start Master, Slaves and Sentinel services respectively from Windows Services (services can be opened by through run [windows key + R] by giving services.msc)
The status of Sentinel can be checked through redis-cli using given below command:
redis-cli -p 26379 info sentinel
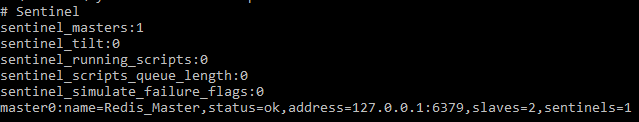
As you see, Sentinel is monitoring ‘Redis_Master’ and its status is Ok.
To know the current master, the following command can be used:
redis-cli –p 26379 sentinel get-master-addr-by-name Redis_Master
![]()
Now stop Redis_Master service from Windows Services. Execute the above command again after 30 seconds. You can see that one of the slaves is re-configured as Master.
![]()
As we all know, software processes are made of data; every process’ instructions, inputs, runtime state and outputs are data stored somewhere. Whether high-level smart IoT services, web development services or product engineering services, enterprises require a better database, cache, and message broker for processing. Redis is designed to be accessed by trusted clients inside trusted environments and provides quick processing as well as help speed up response times through caching data. Contact us today, if you are willing to scale up your business; we offer Redis hosting and fully managed solutions on a cloud of your choice.